Airport CCTV Surveillance from Viseum®
Viseum Airport F3™ (Find, Fix, and Follow) Software Technology Services
- Viseum’s Airport Surveillance Systems fully optimize any network of cameras. Automatically detect, recognize and follow people from short range to long range. At greater distances than any other Airport Security System.
- Reliably detect with 4 times greater accuracy than any other Airport Surveillance System. In real-world deployments.
- Automatically create and grow your secure database of people, vehicles and watchlists. From matching and following just a few hundred people and vehicles. To recognizing many millions in real time.
Viseum Airport Surveillance Systems automatically detect multiple incidents in all directions at the same time. Viseum’s Airport Surveillance and Security Systems operate completely automatically. Following suspects and confirming incidents. With high-quality close-up video even before the alarm is raised. These Airport Security Systems automatically report incidents for rapid response and investigations.
The appearance of Viseum’s Intelligent Airport Surveillance Cameras protecting the airport. This deters criminals because they think every airport surveillance camera is constantly watched.
Intelligent surveillance camera for high security airports
Viseum UK provides the most effective Airport Security Systems. Covering both Perimeter Surveillance and all movement within areas of an airport. Optimized Airport Security use the Viseum Intelligent 360 Security Camera which contains multiple cameras built inside a single unit. Providing complete panoramic coverage in any direction up to 360°. Each Viseum camera in an airport is fitted with the required number of wide contextual view surveillance cameras. For covering the designated areas.
Optimized configuration examples of Airport Surveillance:
- 6 wide contextual view cameras and 1 PTZ Camera for full 360° coverage. Deployed onto airport camera columns.
- 5 wide contextual view cameras and 1 PTZ Camera for 300° coverage. Deployed onto corners of buildings, or airport security lighting columns.
- 3 wide contextual view cameras and 1 PTZ Camera for 180° coverage. Deployed onto the side of airport buildings.
Example Airport Security Systems:
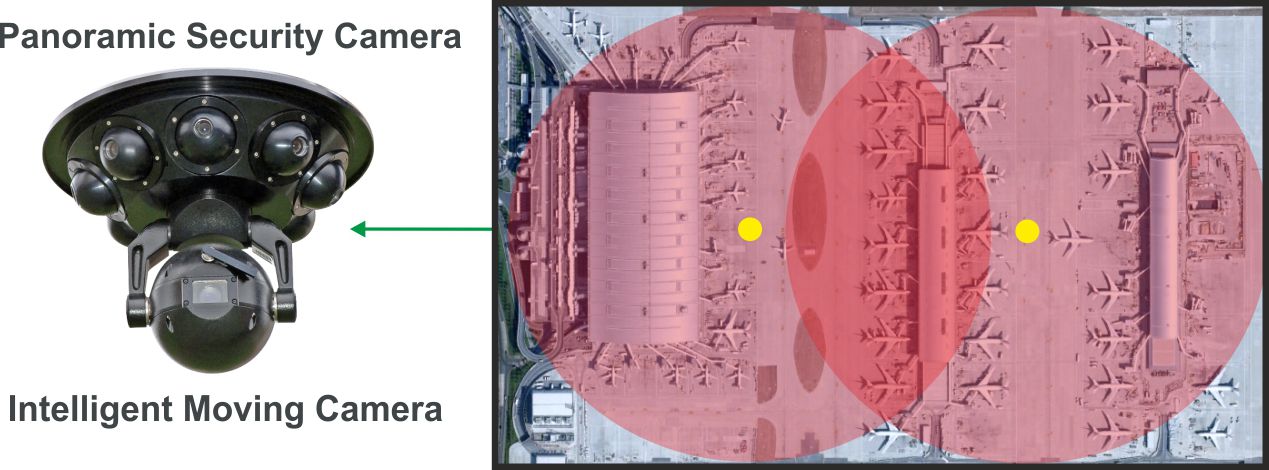
Airport Security Camera Systems protecting 3 airport terminals and 50 aircraft gates.
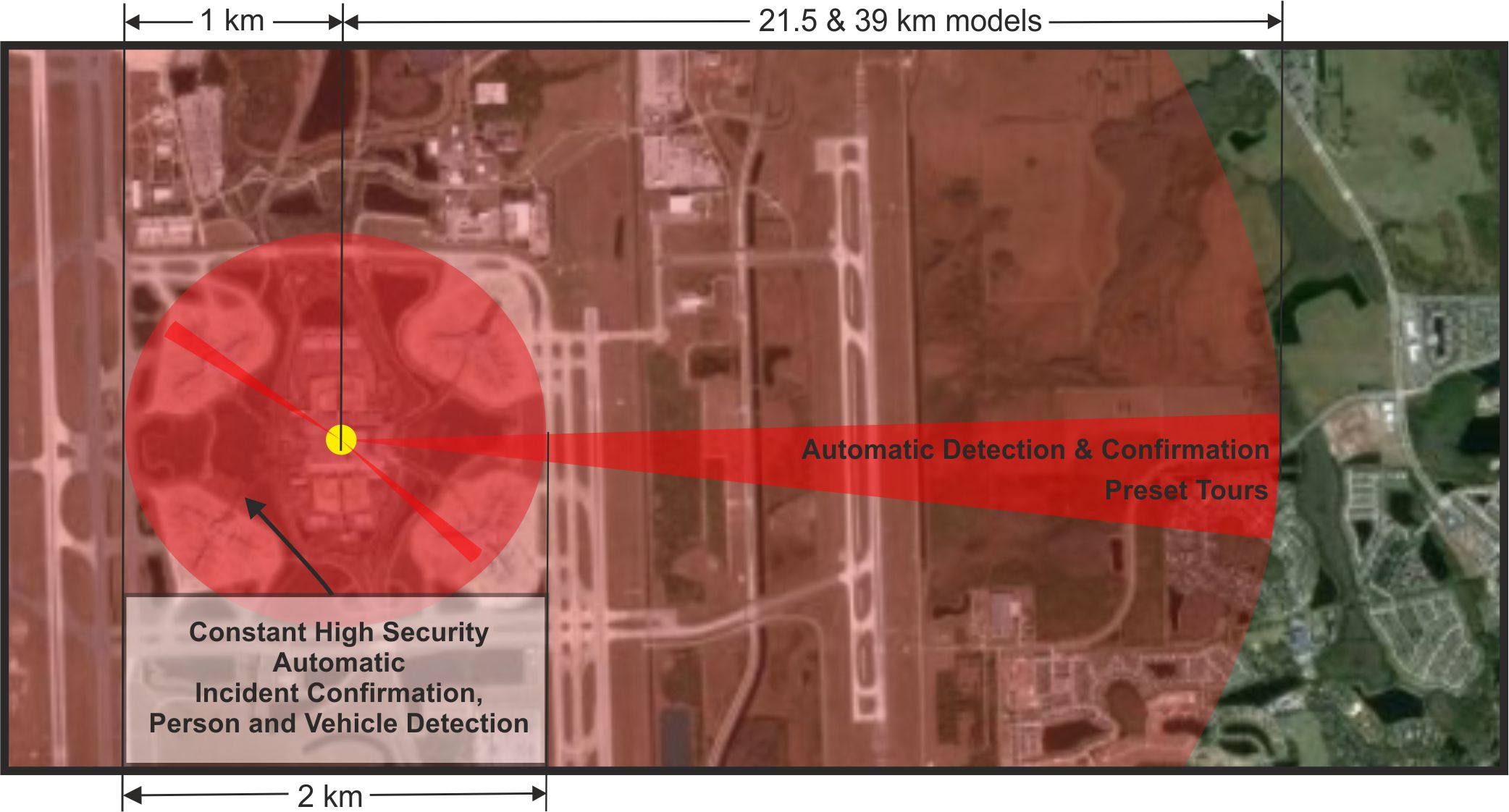
Airport CCTV Extended Thermal surveillance system coverage is customised for each project with distances out to 62 km.
Viseum iVOS™ (Intelligent Virtual Operator Software)
For better use of airport security personnel. Reduce the need to train security staff for routine monitoring tasks. Viseum’s iVOS Software Technology Services monitor each and every camera installed on the network. Analyzing incidents, it automatically controls the PTZ Camera to follow, confirm, record and report incidents. The software also performs key but mundane tasks, such as:
- What airport activity to monitor.

- When to monitor the airport for incidents.
- Where to monitor for airport incidents.
- What responses should follow what types of airport incidents.
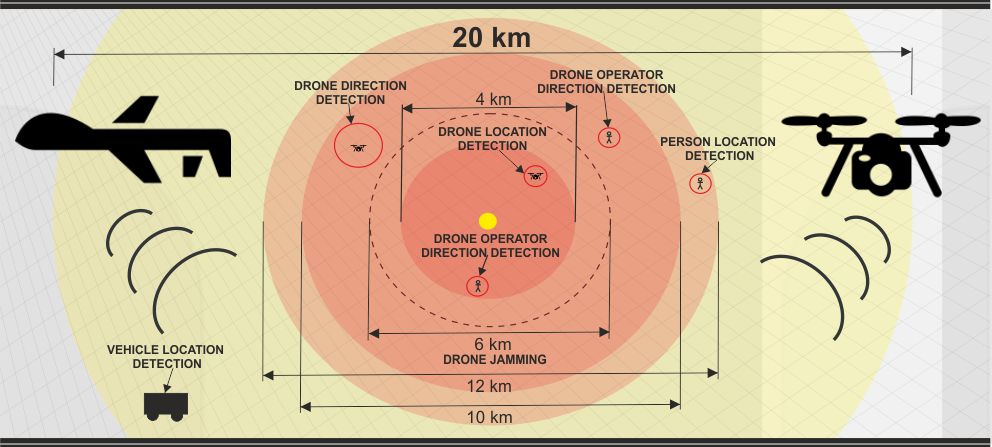
Airport Security and Surveillance Threat Management Systems
If potential intruders approach the airport perimeter fence line. Or if they breach the airport perimeter fence. Viseum’s PTZ Camera automatically zooms into and follows them. Close-up video is then automatically displayed on surveillance monitors for security response. When the airport’s perimeter intrusion detection system (PIDS) is penetrated. Viseum’s iVOS F3 (Find, Fix and Follow) Software Technology Services automatically track intruders. From where they breach the perimeter and circulate. This software will also track the intruders through the airport terminal buildings using the airport’s internal cameras. Tracking them when they move from one camera to another. It will re-identify them if they temporarily disappear and then reappear on other cameras.
If there is more than one intruder within the coverage of a single Viseum IMC, Viseum software will track them and control the PTZ Camera to automatically zoom into, follow, and switch between intruders. Throughout the incident, the intruders’ locations and close-up video images are automatically reported. If suspects enter certain areas, or if security personnel do not follow the correct procedures, the system will automatically notify the head of security. To start escalation procedures.
When the incident has finished, CCTV video is used for rapid investigation. Images of intruders are fed into Viseum software systems to automatically track their movements. Viseum’s face recognition software is used to automatically investigate if the intruders had visited the site before to plan their crime.
Airport Security Baggage System
Our approach for airport security baggage is to visually follow the traveller and traveller’s baggage. When it is with the traveller and when it leaves the traveller for the aircraft’s baggage hold. This tracking uses visual biometrics and cross-checks references with other control devices. It allows the traveller, the traveller’s location and the traveller’s baggage to be automatically reacquainted at the final destination.
This solves many airport security baggage problems and security risks. Including preventing a traveller’s baggage from being collected by the wrong person. Or tampered with. For example, terrorism, mistakes, or theft.
Downloads for Airport CCTV Security Surveillance:
- Viseum iVOS FaceRec Airport CCTV
- Airports Weapon Detection
- Baggage Handling Innovation Examples
- Panoramic Thermal Radar Optical Security Camera
- Intelligent CCTV Thermal and Optical Surveillance
- Panoramic Thermal IMC Security Camera Datasheet
- Solution to Radar and Thermal Systems
- Next Best Thermal Camera Comparison
- Panoramic Security Camera CCTV Design System Architecture

This narrated presentation shows how it is impossible for anyone to identify a weak point of a perimeter that Viseum Thermal and/or Optical Surveillance Cameras are protecting.
 AI Situational Awareness Video Monitoring Software
AI Situational Awareness Video Monitoring Software